When you’re told to include 8+ characters, a number, a capital letter and special characters into your password … you really should. You likely already know how careful you are with passwords, created several many as well but they aren’t just stored on a tiny little sticky note hidden deep in your drawer (that you think no one will find…). They’re stored in giant databases. The question is, how safe are these databases?
Imagine being able to hack into giant databases, there’s millions of user records. But instead of seeing “qwerty123” in the passwords column you see this → $34h$XeG3lQwl$a43MkxP9.
When you type in your password, the system doesn’t store it as it is. Instead, it runs your password through a hash function → which is simply a mathematical algorithm that converts any data into a unique fixed-length string of characters. Think of making a smoothie, you dump a bunch of fruits into a mixer, and your product is this one colour smoothie. Now if you’re able to come up with a way to get the fruit back from that smoothie … please contact us. That’s how the hash function works; it’ll turn your password into what you see as gibberish but is really a combination of random characters. It has 3 features - 1) it’s irreversible 2) the tiniest of changes will change the hash completely 3) same input = same output.
But hey, hackers are pretty smart because if you didn’t realize hashes weren't enough, they did. Hackers know people reuse weak passwords, so they make this huge list of common passwords and their hashes. These lists are called rainbow tables. That’s an instant KO for you and a win for them. The next concept isn’t about adding salt and pepper to your smoothie (I’m not stopping you from trying that out though), it’s about techniques that save security engineers from being fired … or keep your password safe.
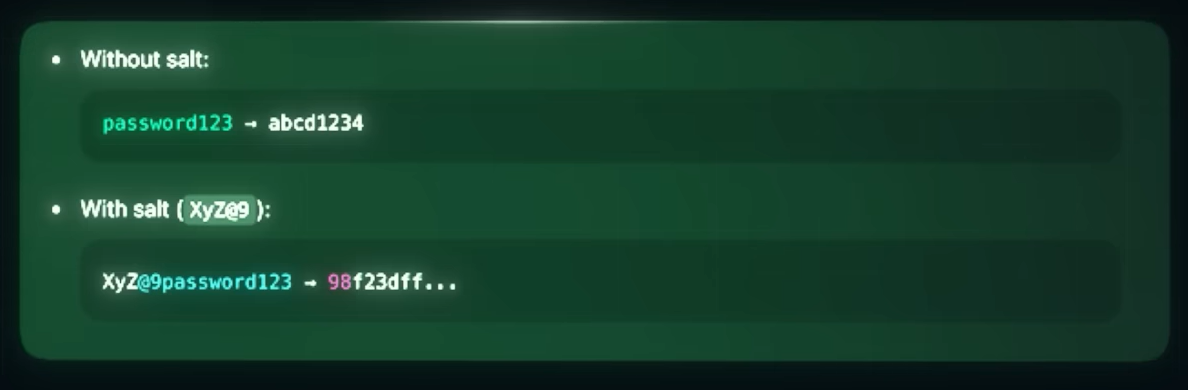
Systems add something called “salt” to the hash and it’s simply just a random string of characters that’s added to your password before hashing takes place. This solves 2 problems - 2 users having the same password and rainbow tables.
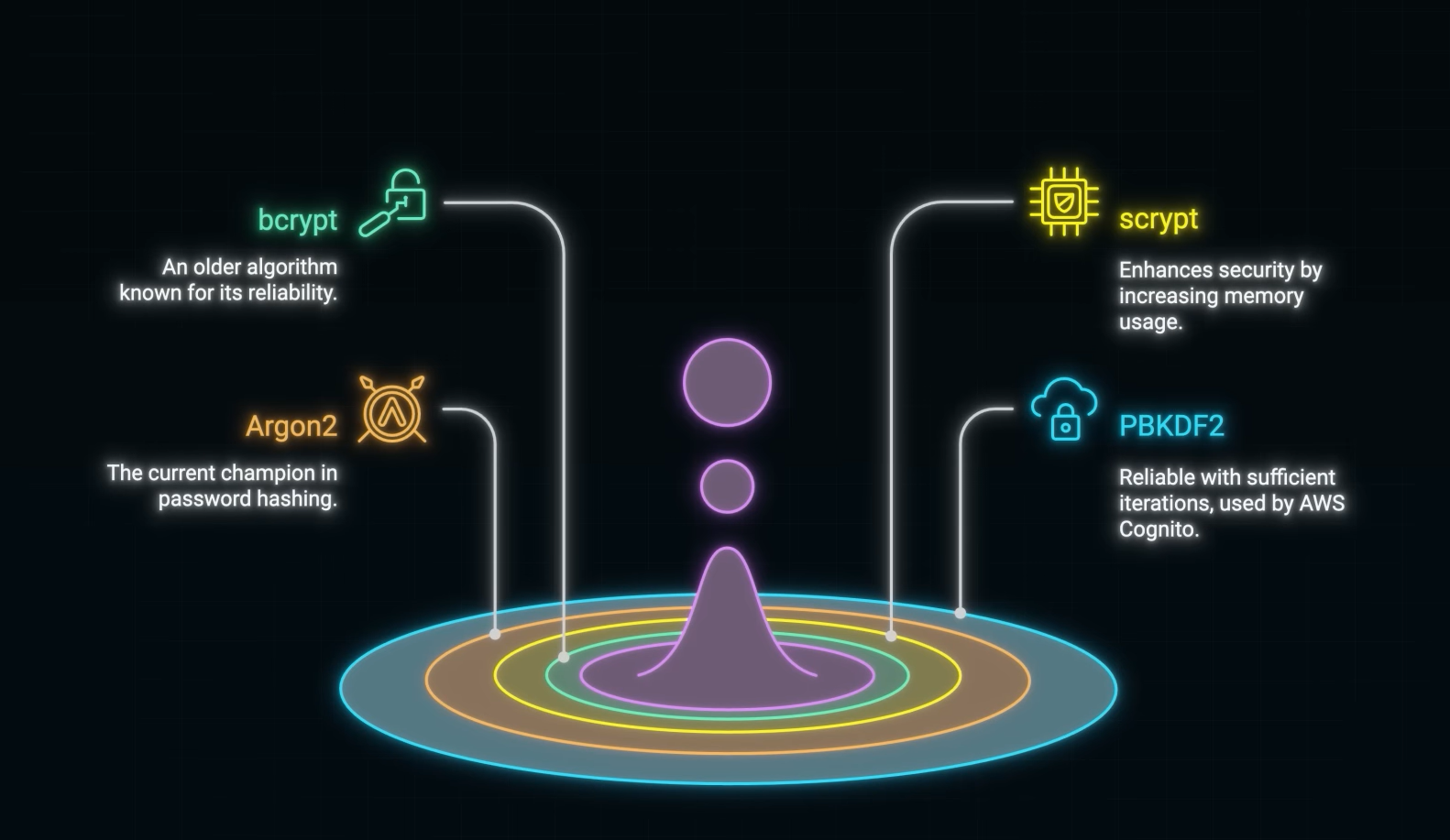
Adaptive Hashing Algorithms (AHA) like bcrypt and argon2 are hashing algorithms that consume time and memory making it harder for the attacker to guess your password. Third, “pepper” is a secret value that’s stored externally, like in a hardware security module … Google and Amazon definitely use peppering (as mentioned in their security guidelines).
Just know password security isn’t about making it impossible for hackers to hack your password but more about making it so impractical and exhausting that they give up.




